Cybersecurity is what we do
Acclaim has worked with leading Cybersecurity vendors for over 25 years to ensure our client have the best security protection available. Cybersecurity is an evolving and ever-changing requirement for all business and threats exist at every level of the IT chain.
From your company website, eCommerce solution, internet gateway, firewalls, modems, servers, individual workstations, connected devices and remote or work from home connections – security threats are an ever-present reality of today’s connected businesses and a variety of products are used as stand-alone solutions or in combinations as complementary elements of the complex cybersecurity puzzle.
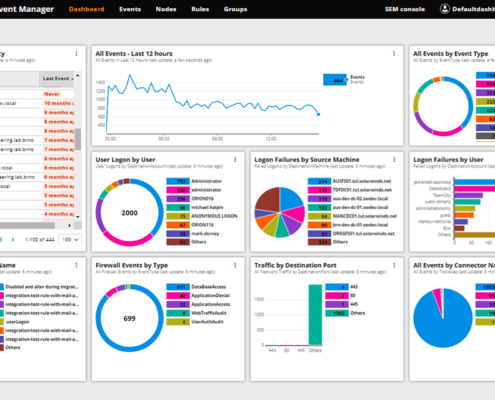
1. Active system and threat management
When keeping your systems secure, its just not possible to rely on a passive “set and forget” approach to putting cybersecurity measures in place.
Hackers and cybercriminals often rely on known exploits – vulnerabilities that may have been identified and resolved already by the software (or hardware) provider. These fixes are then made available as updates to the software, patches or “hot fixes”, or as recommended changes to system settings.

Although a lot of applications auto-update to mitigate this issue, it’s not enough to rely on this feature.
Not all vulnerable software will auto-update, some are regional issues that require manual selection, some updates may fail and others may have further consequences that need consideration. There is also the human factor, whereby users may disable or postpone updates that then present a critical security risk to your business.
Monitoring and securing all vulnerable areas should be done regularly and systematically to ensure the best possible protection.
Similarly backups are often not considered until they are needed, but they are often just automated without a second thought, or worse, a task relying on swapping outdated and untested tapes or removable media.
Backups are often your last line of defence against corruption or ransomware and as such they should be monitored and test restored regularly.
A structured plan, incorporating all of the elements listed here and below should be tailored to mitigate any cyber threat before it can harm your business.
2. Anti Virus and Anti Malware
With seemingly new ways of hacking, stealing, ransoming or just destroying your precious data appearing every day, Eset has been at the forefront of combating these threats, and has remained Acclaims most recommended anti-virus/anti-malware solution for over 10 years.
ESET Endpoint Security for Windows
Leverages a multilayered approach that utilizes multiple technologies in dynamic equilibrium to constantly balance performance, detection and false positives enabling organizations to:
- Protect against ransomware
- Block targeted attacks
- Prevent data breaches
- Stop file-less attacks
- Detect advanced persistent threats
- URL filtering
3. Acclaim Backup
Yes, data volumes are growing, but online backup doesn’t have to be expensive or difficult.
Simplify your approach with Acclaims Cloud Backup solution. Scale with the growth of your data and make sure your business data is protected.
Scheduled to suit your requirements, with on-premise and local-to-cloud options available, Acclaim Backup is the total backup and recovery solution.
Minimise human error and improve efficiency
Outsmart ransomware with direct-to-cloud backups
Back up more frequently, and archive data longer
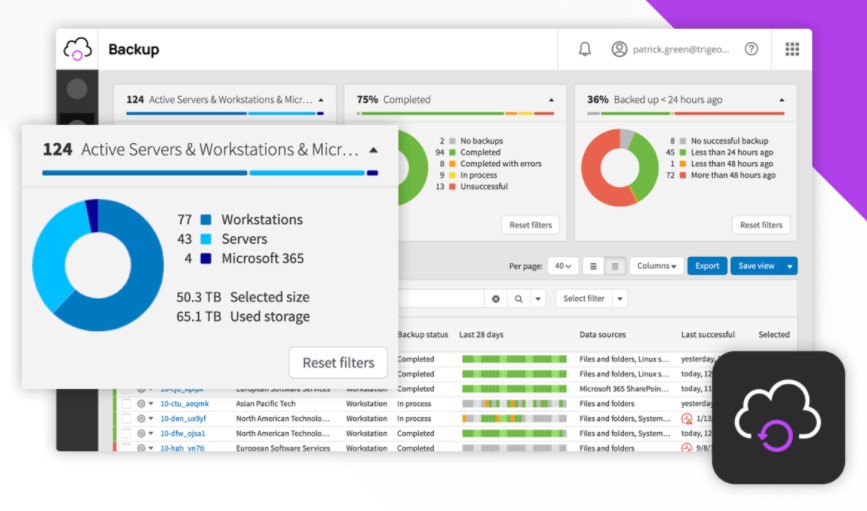
- Physical and virtual server backup
- Backup documents
- Backup for Microsoft 365
- Faster backups and restores
- Bare metal recovery
- Recovery testing
- Security-focused storage
4. Office365 Data Protection

Compromised emails and attachments have long been the hackers preferred method of gaining entry to your systems and data, but further to this, hackers and cybercriminals will also target administrative accounts in their attacks in order to gain access to elevated privileges. The centralised administration model in Microsoft 365 allows all administrators to have global credentials, which grant access to every user’s account and content. If hackers manage to take over a global admin account, they can change critical settings, steal valuable data and leave backdoors to enter again.
There are several areas where inadequate setup, administration and monitoring of your Office365 environment can lead to compromised security and we recommend discussing the available options and putting a monitored security plan in place. A considered approach should include the following steps;
Set up multi-factor authentication (MFA)
To reduce the risk of these powerful accounts being compromised, you can set up multi-factor authentication (MFA) in the Security and Compliance Centre.
Utilise Microsoft 365 built-in data loss prevention (DLP) and email encryption
The DLP tools include multi-factor authentication, dedicated administrator accounts, and malware and ransomware protection for email. Email encryption adds another layer of protection.
Enable Mailbox Auditing
Enable mailbox auditing to monitor activity in Exchange Online.
Use Malware Protection
Microsoft 365 includes some malware protection. You can further strengthen security by blocking file types common to malware.
Defend Against Ransomware
Use Microsoft 365 mail flow rules to block extensions commonly used for ransomware insertion, warn users about email attachments that might be infected, and eliminate auto-forwarding of email.
Encrypt Email
Microsoft 365 Message Encryption is turned on by default. It allows users to send and receive encrypted email messages, both within and outside the organisation. Encryption ensures only the intended recipient can view email content. You have several options available to control how and when email may be viewed, labelled and forwarded.
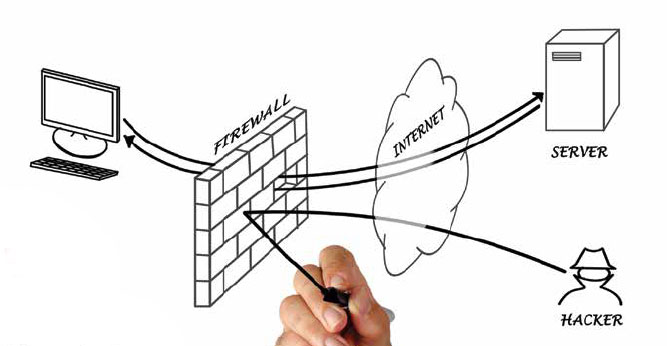
5. Hardware security – Firewalls and Routers
Acclaim works with leading brands such as Sophos, Draytek, Solarwinds and Fortinet to ensure that you have the best network hardware security available.
A firewall (either a separate appliance, or as part of a security grade router) is an essential part of your organisations security system. Without it, your network is open to threats. A firewall keeps destructive and disruptive forces out, and controls the incoming and outgoing network traffic based on security parameters that can be controlled and refined to suit your environment.
An effective firewall will control both inbound and outbound internet traffic. This means you can choose to block access to specific websites within your network as well as blocking malicious content from outside your network. For example, you can protect employees from accessing potentially harmful or unsafe websites that could lead to your network being infected with malware. You can also choose to block inappropriate or non-work-related websites, therefore enhancing the overall productivity of your employees.
An effective firewall will protect your business from:
Remote login
Cyber criminals have the tools to login to your devices remotely. They can then control the device, steal information, or install, ransomware, malicious programs and spyware. An effective firewall will help protect against unauthorised access to your devices via the internet.
Email session hijacking
If cyber criminals gain unauthorised access to your network, they can hijack your SMTP server. This means they’re able to send spam or malicious emails, requests for money or invoices to your contacts via your email server. This could damage your reputation, causing clients to lose faith in your brand and its security. An effective firewall helps protect against email session hijacking, ensuring the valuable relationships that you have with clients and suppliers are preserved.
Application and operating system backdoor vulnerabilities
Certain programs and applications could give cyber criminals remote access to your network via features or bugs, giving them control over the program and putting your employees and data at risk. A firewall will help block hidden access and ensure your applications are secure.
Denial of service
Denial of service is a specific, disruptive attack that could penetrate your server. In this instance, your server would receive a request to connect. When the server attempts to respond, it cannot find the system that made the request. If your server is repeatedly hit with these types of connections, it could slow them down considerably and cause them to crash, meaning your productivity is disrupted. An effective firewall will prevent these kind of attacks from occurring, ensuring your server isn’t slowed down by disingenuous requests.
Email bombs
Similar to a denial of service attack, an email bomb sends the same message to an address on a server so many times that it causes the server to crash. Again, an effective firewall will prevent these attacks and ensure your team can continue to work without disruption.
Malicious macros
A macro is a rule or pattern that determines how an application will run. Cyber criminals can create macros that tell your applications to do things that you don’t want them to, such as delete data or crash the computer. An effective firewall will block these attacks, keeping your data safe and productivity maximised.
Viruses
Viruses are extremely common and can cause serious disruption to businesses. Viruses can spread extremely quickly through networks and emails, often carrying out unwanted activity such as monitor your activity, slow down your device, delete data or lock or crash your device. An effective firewall will block viruses before they can infiltrate your network, protecting your devices from becoming infected with malicious software.
Cyber criminals can easily probe every computer connected to the internet and attempt to penetrate their systems. Without a firewall, they can gain access to your important files, depositing them, removing them or using them maliciously.
A properly configured, maintained, and monitored firewall will protect your data, network, and devices. Importantly, you need to ensure that your firewall has the power to manage normal and encrypted internet traffic without slowing down your devices or compromising security.
Is it time to review your cybersecurity? Why not get in touch to arrange a review.

KNOWING THEIR NUMBERS BECOMES PLAIN SAILING AT DOYLE SAILS

MYOB provides greater efficiency to aid dramatic rise of unique brewery

More visibility has resulted in increased confidence.

Automatic Systems Revolutionised
Have a project in mind?
Why not get in touch? We’re always keen to catch up for a chat to see how our solutions can fit with your business.

Acclaim Group
Contact Details
Unit 4, 6-8 Omega Street
Albany, Auckland
Phone: +64 9 415 0984
Email: sales@acclaimgroup.co.nz

